10 Security Holes Your Website May Face And How To Fix Them
Updated 28 Aug 2023
12 Min
4672 Views
Do you think your website is reliably secured? Perhaps it is indeed. But world statistic data reveals disappointing results to us: the number of hacked websites in 2016 increased by 32% compared to 2015, according to Hosting Facts. Moreover, analysts forecast that the cost of global ransomware damage will exceed $5 billion USD by the end of this year. And world IT giants like Google make sure that the number of hacked websites will greatly be reduced in the near future.
Secure and performant web products development takes more than a major. If it is not protected, it will be a tidbit for any hackers. So what can you undertake to avoid it? Find it out in our article.
Why is website security important?
Everybody protects his or her website since web security is the first point any should pay attention to. And it doesn't matter which type of website they have - business or entertaining. So why do website owners protect it? There are a few reasons as follows:
- To protect the website from viruses and malware;
- To protect users from phishing emails that can be sent using the website;
- To draw more visitors since they all want to feel safe on the website;
- To obtain a higher rank in the search engines;
- To protect a website from hackers and prevent them from stealing important data.
See how machine learning protects your software. Read How can machine learning protect your FinTech app from fraudulent attacks?
As a rule, websites are not hacked purposefully. A modern website comprises of many complicated software components.
Website should be secure on any device
Hackers are using scripts that scan websites for vulnerabilities. If the system is not protected, hacking your website can be a matter of time.
What to do if the website is hacked?
The use of your website for stealing confidential information is one the worst scenarios. But in some cases, it is hacked for sending spam, infecting users' computers. As a result, search engines deny access to the website for users, notifying the owner about the website infection. Website attendance comes to naught, and it can even be removed from search engines.
But the worst scenario is when neither owner nor visitors are aware of the hacking, and malware is infecting users' devices, stealing their data like logins, passwords, banking card data etc.
As a result, you lost your time, money, reputation and clients' loyalty. You bear losses only because you didn't attach importance or ignored the security issues of your business tool.
So, how to know if the website is secure? We prepared 10 main hints you need to get acquainted with and follow them.
10 hints how to secure your website
You should read it carefully since one mistake can cause big trouble. So it's all in your hands.
Update your software
This advice may seem banal, but timely software updates can help you protect your website. It refers both to server software and to any software that can run on your website. Once there are any security holes - hackers are already right here.
In most cases, hosting services should take care of the server software update so it won't be your headache as to how to secure a website. But you should always be alert.
If you use 3rd party software, make sure that your version is up-to-date. Although such services always inform you about a new update.
Protect website from SQL injections
This is the hacking attack when a hacker uses a web form field or URL string parameters to get and control data stored in the database. When somebody is using ordinary SQL queries, a malefactor can input maleficent code that can change tables, change information or delete information.
A new parameter will allow the hacker to add requests at the end of SQL query that will be implemented.
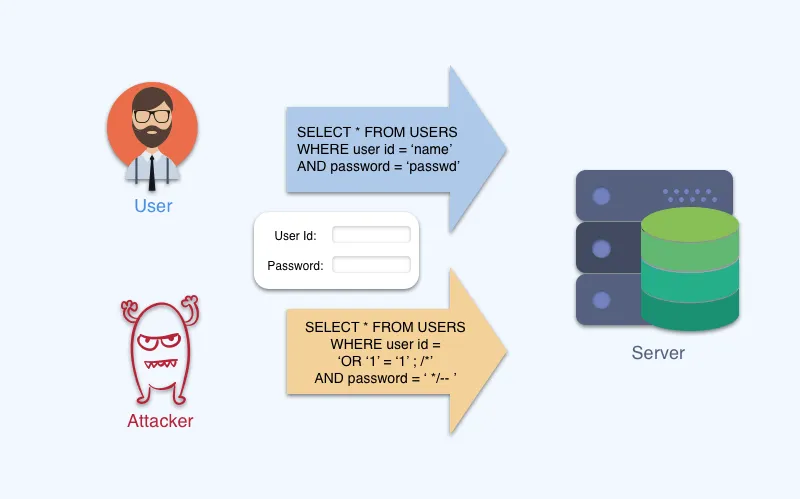
How SQL injection attacks your website
But you can avoid it by always using parameterized queries. It will be enough for website protection from SQL attacks.
Cross Site Scripting (XSS)
XSS is an attack when a hacker tries to run maleficent code for website visitors. You should double-check that you always verify data, encrypt, crop or remove all third party HTML inclusions.
Find out why payment system protection is important. Read How to secure payments processing: the right payment system for your business
Stealing cookies is the most widely spread example of a XSS attack. Websites sometimes store valuable data in cookies, and it can even be the login or password of a user. But active session stealing is the most serious type of XSS attack. So you and your users should always log out, even if it is a home PC, to provide a high level of website security.
Error messages
Be careful when you add a lot of info in your error messages. For instance, you try to log in on a certain website. Here you should use common notifications like 'Invalid password or username'. Never specify whether the username or password is incorrect since the malefactor will understand that he guessed one field and now can keep on hacking the remained one. So you should never forget to ask yourself 'Why is my website not secure?'
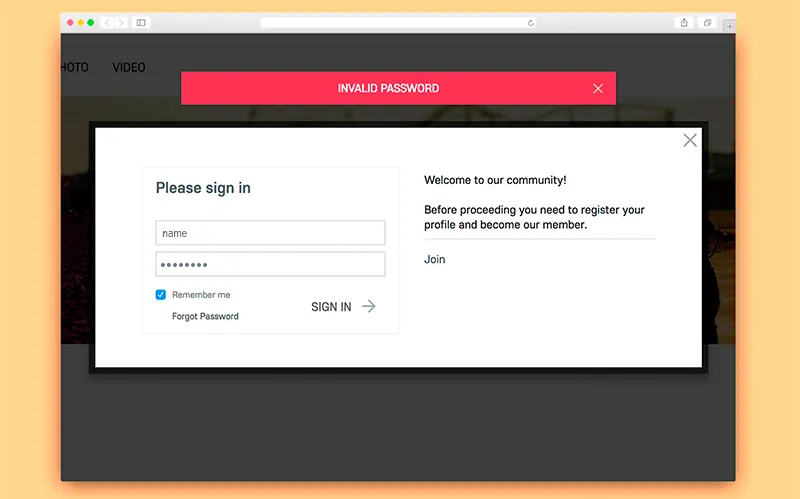
Don't show the malefactor where is the error ocurred
Server-side form validation
Data verification should be made both in the browser and on the server-side. It is possible to catch simple bugs and highlight fields where errors were made. However, this verification may be easily ignored and unverified data will be sent to a server. If a server doesn't verify incoming data, it may lead to undesirable sequences and damage website content protection. Always be on the alert!
Passwords must be secure
Actually, it is not a secret that everybody must use complicated passwords that contain letters and digits. It is critical not only for passwords to admin panels but also for user profiles.
Many users don't like long complicated passwords, however, it is not so difficult - one just needs to create the password not shorter than 6 symbols containing capital and small letters, as well as digits. Such passwords can keep all data safe.
A password should be kept in an encrypted type. You can use SHA (Secure Hash Algorithms). During the authorization process, only encrypted password data will be matched. For additional security, you can use salt. Salt is a method of encryption.
In the case of attack, hackers won't be able to decrypt your password. The only thing he can do is to use software for password selection. If you use salt, passwords will be selected much slower.
Some content management systems (CMS) can provide you with all these features and website protection software. But you should think about additional plugins that will add salt to passwords.
If you are only planning to create your website, you should know how much the development takes. Watch our video!
The cost of website development in 2017
Uploading files
When users upload files to a server, it is a very risky procedure in fact. Even if they simply change the image of a profile. Uploaded files can bring a script that can be implemented on the server if it is opened via the browser.
If you have a form for uploading files, you cannot ignore any file people upload. Unfortunately, file extensions can mislead you easily and if it is a JPEG file, for example, it doesn't mean that it is an image indeed. The extension can be counterfeited.
Even when you open a file and look it through, you will not be able to guarantee a complete protection from replacement. Most images allow to store PHP code that can be implemented on a server.
Files uploading window
What is the solution? Ultimately, we don't need to allow users to run files they uploaded. By the way, bad files often have a double extension like png.php.
You can rename uploading files and change extensions or set file permissions like CHMOD 0666 - file cannot be implemented. Also, you can create a .htaccess file that will prevent running files with double extensions and it will give your website malware protection.
Server security
If you configure a server on your own, you should know some important issues for website and web application security.
- First, make sure you have a firewall installed and all insignificant ports are blocked. If possible, set a DMZ (demilitarized zone) that provides the access to the 80th and 443rd port;
- Second, for loading of files to a server, use only safe methods such as SFTP or SSH;
- Third, run the database on another server. In this case, only your web server will get access to the database. And your files will be protected in a proper way;
And, finally, don't forget about the prohibition of physical access to the server.
SSL protocol
SSL is the protocol that is used for website security on the Internet. All the time when you transfer information between a website and web server, a security certificate is used. But if the means of communication are not secure, malefactors can attack the certificate and get access to users' data.
HTTPS protocol
This protocol is closely connected with SSL since it is transferred via SSL encryption protocol. SSL certificates must be installed for data transmission by HTTPS on the web server. We put this point in the end since all websites today use HTTPS protocol as a website protection service. So it is a must-have feature of your website.
A SSL certificate is one of the main factors of Google ranking so the transition to HTTPS protocol increases website positions in Google search.
Website security testing tools
If you think you did everything from the list above, protected your website as much as you can, that it is time to verify it, the most effective way to do it is to test website security using special tools for assessing vulnerabilities.
There are paid and free services that can help you. They use scripts for hacking your website - such scripts as SQL injections and others. But don't be afraid, these scripts are not dangerous for your website. And it will not hack, it will TRY to hack. If there is any vulnerability, the service let you know.
So, there are a few website security check tools you may want to pay attention to:
Netsparker
There is a free trial version you can use for a start. This service will be good for testing SQL injections and XSS. It works on all websites and web applications regardless of the technologies they were developed with. In the end, you will get a detailed report with all the vulnerabilities of your website if there are any.
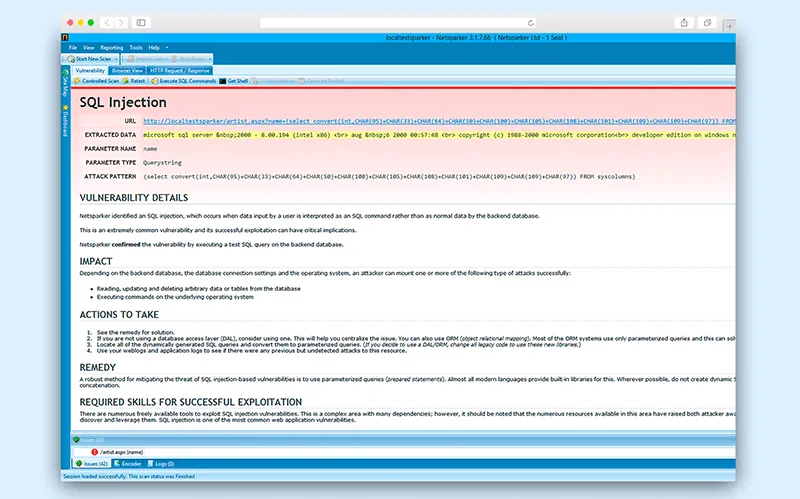
Netsparker is the tool for testing website for SQL injections
OpenVAS
It is one of the most popular website security scan tools that is very good for testing all known vulnerabilities which are more than 25,000. Scanning your website deeply can help you remove all vulnerabilities. But it is rather hard to configure so it won't be acceptable for everybody. It's scanning tool is called Greenbone Security Assistant.
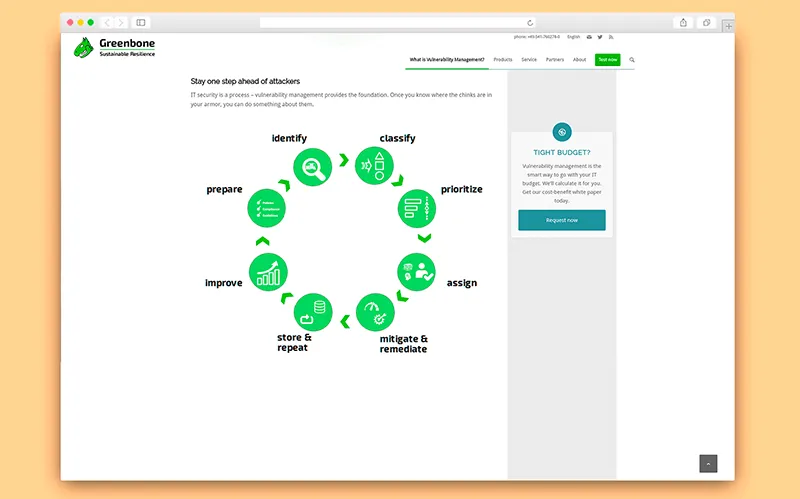
Greenbone: find all know vulnerabilities
Acunetix
The tool for security control of web applications. It allows website owners to detect vulnerabilities in website security systems before a malefactor does it. It can also search for errors in scripts in PHP, ASP.NET and ASP languages. There is a 14-day trial version at your disposal in this web app security testing tool.
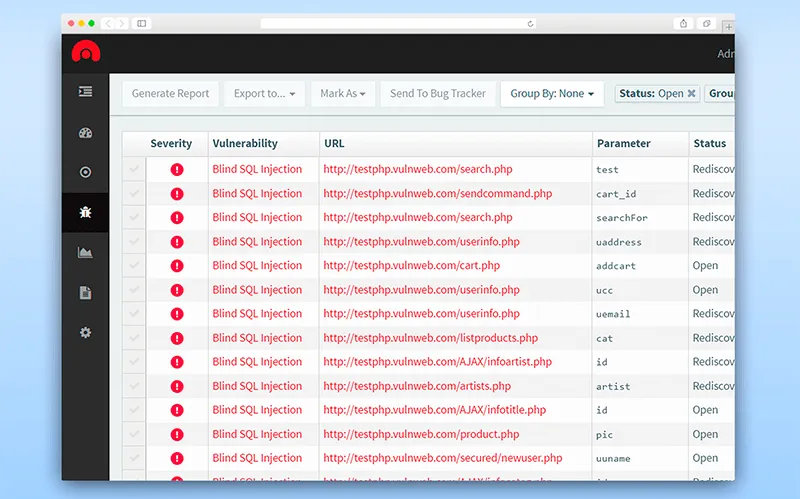
Acunetix tool: find error in scripts
If you are a skilled specialist and good at software development, you can try to hack your website on your own using different scenarios.
How we protect our websites
As you see, the development of the website is not enough. Security is the area you should pay attention to as well. But as for us, we don't ignore this area as well. Neither when we develop new websites not in company's personal website.
So what is a protected website in our opinion and what do we use? As it was noted above, HTTPS protocol is used in any website and cleveroad.com is not the exception to the rule.
In addition, we use CSP technology. CSP means Content Security Policy and it is a mechanism of protection from XSS. But not only XSS, it blocks all attacks with content infiltration. CSP describes safe sources of loading resources, makes it possible to set rules for styles and application scripts. Loading from resources that are not in whitelist are blocked. We use frame-ancestors: 'self' to block loading of our website content in IFrame.
Figure out how mobile security is evolving. Read New authentication methods that shape the future of mobile security
And also we use CloudFlare. It protects our website from DDoS attacks. It is functioning like a reverse proxy. And using this technology, the website is loading much faster and is more secure at the same time.
The security of our website is very important for us. Since it is the face of our company and we always want to be open and reliable for our customers. If you need to provide your software with security, we can do it. Our staff has enough skilled specialists that can help you solve any problem your website may face. Contact us and subscribe to our blog not to miss any useful information!
There are several aspects that you need to consider while creating a secure. Some of them are:
- Keeping your software up-to-date
- Protecting your software from SQL-injections
- Creating secure passwords
To learn more security methods for a website check How To Make A Website Secure.
There are different reasons why your website isn't secure:
- You don't use or use outdated SSL certificate
- You have weak passwords
- You use outdated software that doesn't protect users from modern threats
To learn more about threats to your website check our article on website security.
The easiest way to know that the website is secure is to check the SSL certificate. If you see a lock to the left of the website's URL, it means that the website is encrypted. An SSL certificate grants that the communication with the website is encrypted, and hackers can't intercept the data from the communication channel. Still, users of these websites can fall victim to social engineering and fishing, so you should stay cautious even with the SSL certificate.
Any website needs to be secured. Websites that gather user data should protect this information. Data leaks may lead to large fines and even criminal liability. Websites that don't process user data still should be protected because websites may be hacked and display inappropriate information.
If a website isn't secure, it may be hacked by fraudsters for their own interests. In case your website stores personal information, leaks to third-parties may lead to fines and criminal liability. In other cases, the website may be hacked and display malicious content. That's why you need to protect your website in order to save your brand image and customer loyalty.
The primary tool in cybersecurity is programming. To make your website secure, you need to foresee possible threats and protect your users by yourself. Besides, companies implement various protocols like PCI DSS for credit card data security or HIPAA for protecting personal health information. On top of that, third-party antivirus software is also important for website security.

Evgeniy Altynpara is a CTO and member of the Forbes Councils’ community of tech professionals. He is an expert in software development and technological entrepreneurship and has 10+years of experience in digital transformation consulting in Healthcare, FinTech, Supply Chain and Logistics
Give us your impressions about this article
Give us your impressions about this article