HIPAA Compliance Checklist for Software Development: Tips for Maintaining HIPAA
Updated 29 May 2023
15 Min
1009 Views
HIPAA Compliance is an important consideration for any business that handles health care and medical data. As an experienced IT provider with 10+ years of experience in developing telemedicine software solutions, we at Cleveroad are here to share our expertise and help you understand how to make HIPAA compliant software. Why is it critical?
A small HIPAA offense could end up costing you from $100 to $50,000, loss of reputation, or even jail time. So it's best to comply with this law right from the start. To ensure that HIPAA compliant software development will be fulfilled accurately, it is crucial to prioritize the confidentiality, integrity, and accessibility of PHI.
In a nutshell, deciding to build HIPAA compliant software, you should fulfill the following requirements:
- Protect medical data from unauthorized parties or users in a reasonable manner
- Ensure that PHI and ePHI cannot be altered or deleted without authorization
- Make health records accessible to authorized users via software integration
- Control anticipated security risks and deploy protection measures
- Provide essential role-based controls and data management tools
By meeting these requirements, your software will be HIPAA compliant and will guarantee the confidentiality, integrity, and availability of PHI. But how to make software HIPAA compliant, and what this regulation implies? Let’s find it out in our comprehensive guide.
When Your Software Needs HIPAA Compliance
Let’s begin with the fundamental notions. HIPAA (Health Insurance Portability and Accountability Act) is a federal law that was enacted in 1996 to protect the privacy and security of sensitive patient health information, also known as PHI (Protected Health Information). The act outlines a set of regulations and standards that dictate how healthcare providers, health plans, and healthcare clearinghouses must safeguard PHI. HIPAA also applies to any software vendors that create solutions for the healthcare industry that process, store, or transmit PHI electronically.
Compliance helps to ensure that PHI and ePHI are protected from unauthorized access, disclosure, alteration, or destruction. It also helps to establish trust and confidence among patients and medical providers, which is crucial in the healthcare industry.
Keith Rabbin
Senior Security Consultant at Cisco
The statutes for criminal prosecution have been in HIPAA for a very long time, but they have not been put to use very often. Large monetary penalties have made headlines over the years. Now, it appears that criminal convictions are also something to take seriously.
So, when does your software need to be HIPAA compliant? If your software processes, stores, or transmits PHI electronically, it must be HIPAA compliant. This includes any software that is integrated with a healthcare organization's electronic health records (EHR) system or that handles PHI in any other way.
To ensure that your software is HIPAA compliant, it must meet certain criteria:
First, it must safeguard PHI's confidentiality, integrity, and availability. This means that medical data must be reasonably protected from unauthorized parties or users, PHI cannot be altered or deleted without authorization, and health records must be easily accessible to authorized users through integrated solutions like EHR or patient/medical employee portals.
Second, your software must control all reasonably anticipated security risks and deploy necessary protection measures, including data operations such as data exchange, storage, copying, and others. This includes implementing access controls, such as user authentication and authorization, and ensuring data is encrypted during transmission and storage.
Finally, HIPAA compliant software development must provide essential role-based controls and data management tools within a user-friendly interface to authorized users. This ensures that healthcare providers can easily manage and access PHI as needed.
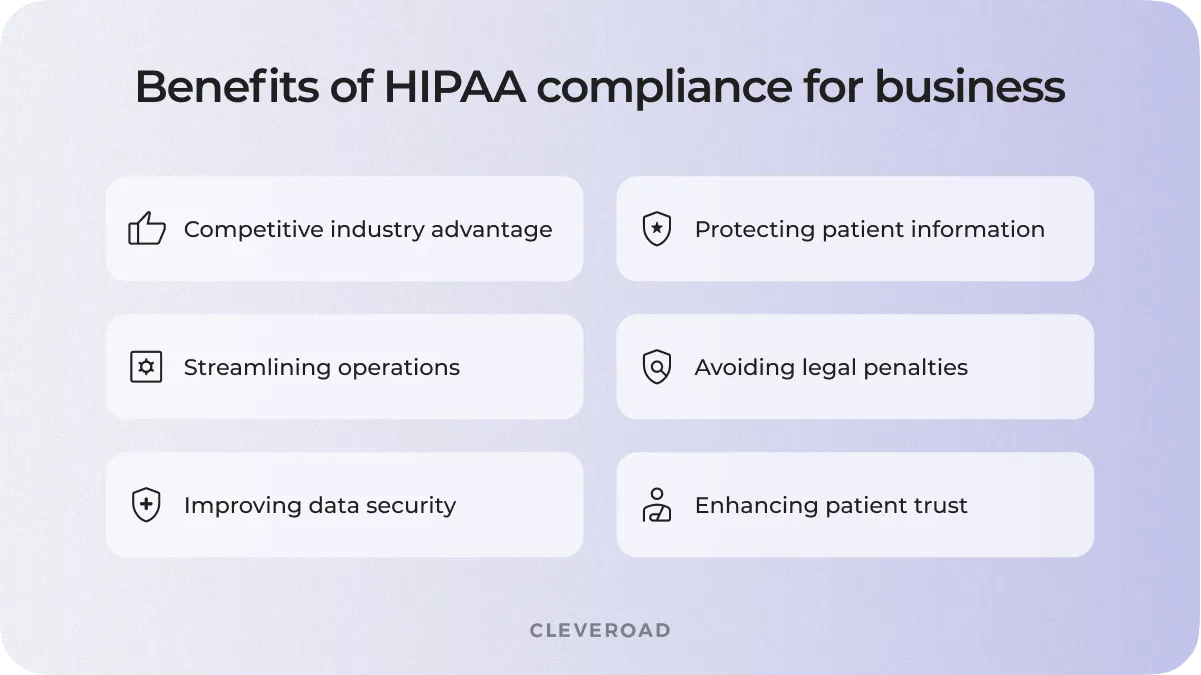
Why is it essential to comply with HIPAA?
The following list indicates the parties that is mandated for HIPAA requirements:
- Healthcare providers include doctors, nurses, psychologists, dentists, chiropractors, and other individuals or entities that provide healthcare services. This includes hospitals, clinics, nursing homes, and other healthcare facilities. HIPAA requires healthcare providers to protect patients' health information, whether stored in paper records or electronically.
- Health plans include insurance companies, health maintenance organizations (HMOs), and other organizations that pay for healthcare services. This includes both private and public health plans, such as Medicare and Medicaid. HIPAA requires health plans to protect the privacy of their members' health information, including their medical records, insurance claims, and payment information.
- Healthcare clearinghouses are entities that process healthcare transactions, such as billing and claims processing, for healthcare providers and health plans. Examples of healthcare clearinghouses include companies that provide medical billing services or electronic health record (EHR) software. HIPAA requires healthcare clearinghouses to protect the privacy and security of the healthcare information they process.
In addition to these primary entities, HIPAA also applies to their business associates. Business associates are individuals or entities that provide services to healthcare providers, health plans, or healthcare clearinghouses that involve access to patient's health information. Examples of business associates include billing companies, IT support companies, and law firms that provide legal services to healthcare providers. HIPAA requires business associates to sign a contract with the covered entity stating that they will comply with HIPAA's privacy and security requirements.
Explore more details about HIPAA compliance in our guide
When it comes to HIPAA compliance for soft dev, there are certain criteria you should consider depending on the following:
Type of entity
A covered Entity (CE) is any entity that provides medical services or performs medical information processing operations, such as physician practices, hospitals, insurance companies, etc. If the software is used as a tool to process, store and transmit medical information, it is CE, and the software must be HIPAA compliant.
A Business Associate (BA) is any organization that processes health information on behalf of or for CE. For example, it could be third-party service providers such as IT companies, consulting firms, etc. If the software is used to process medical information on behalf of or for CE, it is BA, and the software must also be HIPAA compliant.
Data type
Protected Health Information (PHI) is any information that identifies a patient and is related to their health or medical history, such as name, address, social security number, medical history, test results, medications, diagnoses, etc. The software falls under HIPAA compliance if it contains PHI. Electronic Protected Health Information (ePHI) is any PHI that is stored, processed, or transmitted electronically. To illustrate, it could be an electronic medical record (EMR), electronic prescriptions, electronic insurance claims, etc. Software must be HIPAA compliant if it processes, stores, or transmits ePHI.
Software solution type
Electronic Medical Records/Electronic Health Records (EMR/EHR) is health information storage software used for patient management, health care delivery, or medical practice support. EMR/EHRs must be HIPAA compliant because they contain PHI and ePHI.
Personal Health Records (PHR) is software that allows patients to store their personal health information and share it with healthcare providers as they see fit. PHRs must also be HIPAA compliant because they contain PHI and ePHI.
Health Information Exchange (HIE) is software that allows healthcare providers to share health information about patients. HIEs must be HIPAA compliant because they process and transmit ePHI.
Telemedicine software development makes it possible to conduct medical consultations and examinations remotely using communication technology. Telemedicine must be HIPAA compliant because they process and transmit ePHI. It is important to note that to be HIPAA compliant, a comprehensive approach must be taken, and all aspects related to processing, storing, and transmitting medical information must be considered. In addition, HIPAA compliance should be viewed as an ongoing process rather than a one-time event.
HIPAA Compliance Checklist For Software Development: Guidelines to Follow
Answering how to make HIPAA compliant software and ensure that your platform meets all privacy and security requirements, a number of recommendations must be followed, including the following activities below:
User authorization
One of the most important aspects of HIPAA Compliance is restricting access to PHI to authorized users only. This requires the use of user authentication and authorization mechanisms on the platform. This includes creating unique accounts for each user, using strong passwords, and multi-factor authentication. In addition, platform administrators should be able to manage user accounts, such as disabling access for inactive users and assigning access levels based on user roles.
Remediation plan
The next important aspect is the development of a remediation plan after a security breach. This includes defining the steps to be taken if the system has been compromised or data has been leaked. The recovery plan should include procedures for notifying users and regulators and actions to address the causes of the security breach.
Emergency mode
In addition, the platform must have an emergency stop mode that allows quick access to the PHI in the event of an emergency, such as a security breach or natural disaster. Emergency Mode should only be available to authorized platform administrators.
Activity monitoring
The platform must have mechanisms to monitor user activity and audit access to PHI. This includes the maintenance of audit logs that record all user activities related to PHI access. In addition, the platform must have mechanisms for monitoring network activity and detecting anomalies that may indicate a security breach.
Data backup
An important aspect is to regularly back up the data that is stored on the platform. An important aspect is to regularly back up the data that is stored on the platform. Backups should be created regularly, such as daily or weekly, and stored in a secure location where they will be protected from loss, damage, or unauthorized access. In addition, regular checks should be made on the integrity and availability of backup data to ensure that it can be restored if needed.
| Points to consider and implement | Practices to fulfillment |
Data access management |
|
Performance verification |
|
Product integrity |
|
Anti-tampering program |
|
Credible user authentication |
|
Protected data transferring |
|
In general, following these guidelines will help ensure that the platform is HIPAA Compliance. However, keep in mind that HIPAA Compliance is a dynamic process, and security policies and procedures must be continually updated and improved to protect PHI.
How to Make Software HIPAA Compliant: Steps to Follow
Here are the steps required to execute to get high-quality HIPAA compliant software as an output:
The first step in creating HIPAA-compliant software is to find a vendor with healthcare expertise and knowledge of HIPAA requirements. This will save you the time and effort required to learn all of the HIPAA Compliance requirements and build the appropriate solution from the ground up. If you have found a vendor that has experience with projects that require HIPAA compliance, then it’s a perfect option to choose a partner with deep domain expertise. This ensures that the vendor is familiar with laws requirements and knows how to implement them in the software.
To illustrate, the Cleveroad team has successfully developed a HIPAA-compliant solution — clinic management system for a US-based rehab clinic. One of the key priorities of this project was to ensure safe medical data migration from the previous EMR system while also maintaining compliance with HIPAA requirements. We carefully designed and implemented the new system with HIPAA regulations in mind, ensuring that all patient data is kept secure and confidential.
Moving forward, let’s consider which steps should be taken to implement a HIPAA-compliant solution in the example of Cleveroad software development lifecycle (SDLC).
Step 1. Solution design stage
During this stage, we work with you to define the core aims of your project and gain a clear understanding of your business context. From there, we schedule a meeting with our Solution Team to dive deeper into your project and clarify your requirements. Our Solution Design team, which typically includes business analysts (BAs), a solution architect (SA), and a designer if necessary, will process your application and preliminary information. This team works closely with you to define your business demands and deliver a rough estimate for your project. This comprehensive approach ensures that we fully understand your needs and deliver a healthcare solution that meets your expectations.
Step 2. Discovery phase
Discovery phase (also known as the analysis and planning stage) is an essential step to define tech and business requirements before moving to the coding stage. It’s required to create a clear plan for project implementation, as well as determine HIPAA compliance requirements. A detailed feature list is created, with a business analyst leading the process of writing and agreeing upon the document with the client. Cleveroad's BAs meticulously study project requirements and conduct meetings to address business needs and mitigate potential risks.
Step 3. UI/UX design stage
In this stage, design layouts are created that define the user interface and interaction with the software. The designer should make sure that the UI does not contain sensitive data and meets HIPAA Compliance requirements.
Step 4. Healthcare software development
In this step, functional components of the software are created and tested. Each component must be HIPAA compliant, and all changes must be tested for HIPAA Compliance. Software engineers use secure coding practices to develop an architecture that protects PHI from unauthorized access and ensures data confidentiality, integrity, and availability, implement access controls, encryption, secure data transmission, and other technical safeguards to protect PHI.
Step 5. Release and support
After the development stage, the HIPAA compliant software needs to be released and deployed to the relevant systems. This is an important stage to ensure that the software is properly integrated with existing systems and is working correctly. The deployment process should be conducted in a manner that minimizes disruptions to ongoing operations.
Additionally, post-development support is crucial for HIPAA-compliant software. Support services should be available to promptly address any issues or concerns that may arise, including security incidents or compliance audits. The software vendor should provide regular software updates and maintenance to ensure that the software remains HIPAA compliant and meets the evolving needs of healthcare organizations.
Developing HIPAA compliant software requires a comprehensive approach that considers the healthcare industry's unique requirements. By following the above steps, you can ensure that your products are designed and developed to meet HIPAA standards, thus providing customers with secure and reliable solutions that protect patient data and support their compliance obligations.
Tips to Maintain Persistent HIPAA Compliance
How to build HIPAA compliant software and prolong its lifecycle? To avoid your solution becoming outdated and irrelevant, we highly recommend fulfilling the following procedures on a regular basis:

HIPAA compliance best practices
Infrastructure access management
Ensure employees have access to necessary information and resources without violating HIPAA rules. This may include limiting access to some data and creating accounts only for employees needing it.
Cybersecurity practices implementation
Data protection is a crucial aspect of the entire HIPAA act. Cybersecurity measures such as protecting networks, protecting data from malware, and strengthening access controls should be implemented.
Access operation
Access to sensitive information should be regularly reviewed and restricted to prevent unauthorized access to data. Manage employee accounts, remove inactive accounts, and restrict access to information that is not needed for employee work.
Data encryption
Data encryption is an important component of data protection within the HIPAA software development guidelines. Data should be encrypted during transmission and in storage, ensuring that data is protected in the event of a security breach.
Read our guide which discloses the importance of data security in healthcare as well as the best practices
Data performance management
Data should be monitored regularly, and any changes that may affect HIPAA compliance should be tracked. You also need to verify that the data is current, accurate, and complete and that it can be used in accordance with the law.
Periodic verifications
Regular audits should be conducted to ensure that systems and processes are HIPAA compliant. Audits may include reviews of policies and procedures, access controls, data encryption, and other cybersecurity measures.
Specialists’ training
Training and awareness of employees who work with medical information are key to reflecting the guidelines and regulations of HIPAA. Every employee must understand the importance of medical privacy and be trained in data security and related policies.
Long-term risk assessment
Finally, long-term risk management is also important to maintaining ongoing requirements meeting. This includes regularly updating policies and procedures, reviewing policies and procedures when there are any changes in the law, and continuously monitoring security systems and detecting potential risks.
HIPAA compliance for software is a complex process that requires not only initial compliance but also ongoing monitoring and support. Following these tips will help you maintain ongoing HIPAA compliance and ensure a high level of medical privacy protection. However, the most reliable way of how to make your software HIPAA-compliant and keep it competitive for a long time is by getting a qualified IT services provider with solid domain experience.
HIPAA Compliant Expert Assistance
Cleveroad is your reliable technical partner, ready to boost your business capabilities. Our team of HIPAA compliant software developers possesses strong domain expertise in the healthcare industry and extensive experience in developing telehealth software complying with HIPAA, HITECH, TX-HB300, HL7 integration, CCD, GDPR, and other health-related legislations. We understand that creating HIPAA-compliant software can be a complex process requiring specialized expertise and knowledge, and we are ready to offer our assistance in this matter.
We are confident that with our professional experience in creating HIPAA-compliant software, you'll get a resilient and secure healthcare solution that meets your requirements and mitigates legal risks. Our company is committed to improving healthcare quality through innovative technology, and we are ready to take on any tasks related to developing HIPAA-compliant software and other regulatory standards.
Let us demonstrate our experience in building HIPAA-compliant software so you can understand the value you can get with our service:
Quality Management System for Medical Devices Manufacturers
Our client is a US-based company that provides medical device manufacturers with Total Quality Assurance services. We helped the business to deliver a brand-new Quality Management System to streamline internal operations. One of the team's challenges was ensuring system compatibility with government regulations, namely FDA 21 CFR 820 and 21 CFR 11 and the ISO 13485 requirements. The newly created software was successfully integrated into the company's services. Using it allows manufacturers to meet the FDA and ISO certification requirements for medical devices and their production.
IoT-based System for Monitoring EKG and Blood Oxygen Level
Our customer is a US company that manufactures and sells medical IoT hardware. Our team helped the client to create and develop a HIPAA-compliant IoT-based system for EKG monitoring and checking the oxygen concentration in human blood. We’ve also implemented AES-256 encryption and safe Personal Health Information storing instruments. As a result, our client received a mobile telecare app that meets US health regulators' requirements and provides users with valuable opportunities to track vital signs.
Mental Health Software for Nedley Depression and Anxiety Recovery Program
The mental health app has been designed to be used in conjunction with the Nedley Depression and Anxiety Recovery Program, a program created by Dr. Nedley. The Cleveroad team of certified software engineers delivered an app that provides personalized schedules and activities to help users improve their mental health during a specified timeframe while complying with HIPAA regulations. Our experts have utilized Big Data algorithms to select activities for each user by analyzing data gathered from all users while ensuring that all personal information is kept confidential and secure in accordance with HIPAA guidelines.
If you are looking for a reliable partner for HIPAA-compliant software development, we are here to help. Our team of professionals is ready to take on the challenge and provide you with a robust healthcare improvement solution. Reach us today to discuss your needs and request a call with our HIPAA compliant software development consultants.
Entrust HIPAA software to experts
Ensure the highest healthcare data security with a solution meeting HIPAA standards with Cleveroad
In a nutshell, building HIPAA compliant software, you should fulfill the following requirements:
- Protect medical data from unauthorized parties or users in a reasonable manner.
- Ensure that PHI cannot be altered or deleted without authorization.
- Make health records easily accessible to authorized users through integrated solutions like EHR or patient/medical employee portals.
- Control all reasonably anticipated security risks and deploy necessary protection measures, including data operations such as data exchange, storage, copying, and others.
- Provide essential role-based controls and data management tools within a user-friendly interface to authorized users.
- Step 1: Find an experienced tech vendor
- Step 2: Solution design stage
- Step 3: Discovery
- Step 4: UI/UX design
- Step 5: Development
- Step 6: Release and support
- Ensuring IT infrastructure access
- Implement cybersecurity measures
- Access controls
- Data encryption
- Data performance management
- Regular audits
- Employee training
- Long-term risk management
- Employee training

Evgeniy Altynpara is a CTO and member of the Forbes Councils’ community of tech professionals. He is an expert in software development and technological entrepreneurship and has 10+years of experience in digital transformation consulting in Healthcare, FinTech, Supply Chain and Logistics
Give us your impressions about this article
Give us your impressions about this article
